Use Cases
Here are some examples of what you can do with the Intruder MCP server. These are natural language prompts you'd type into your AI agent, and it handles the API calls behind the scenes.
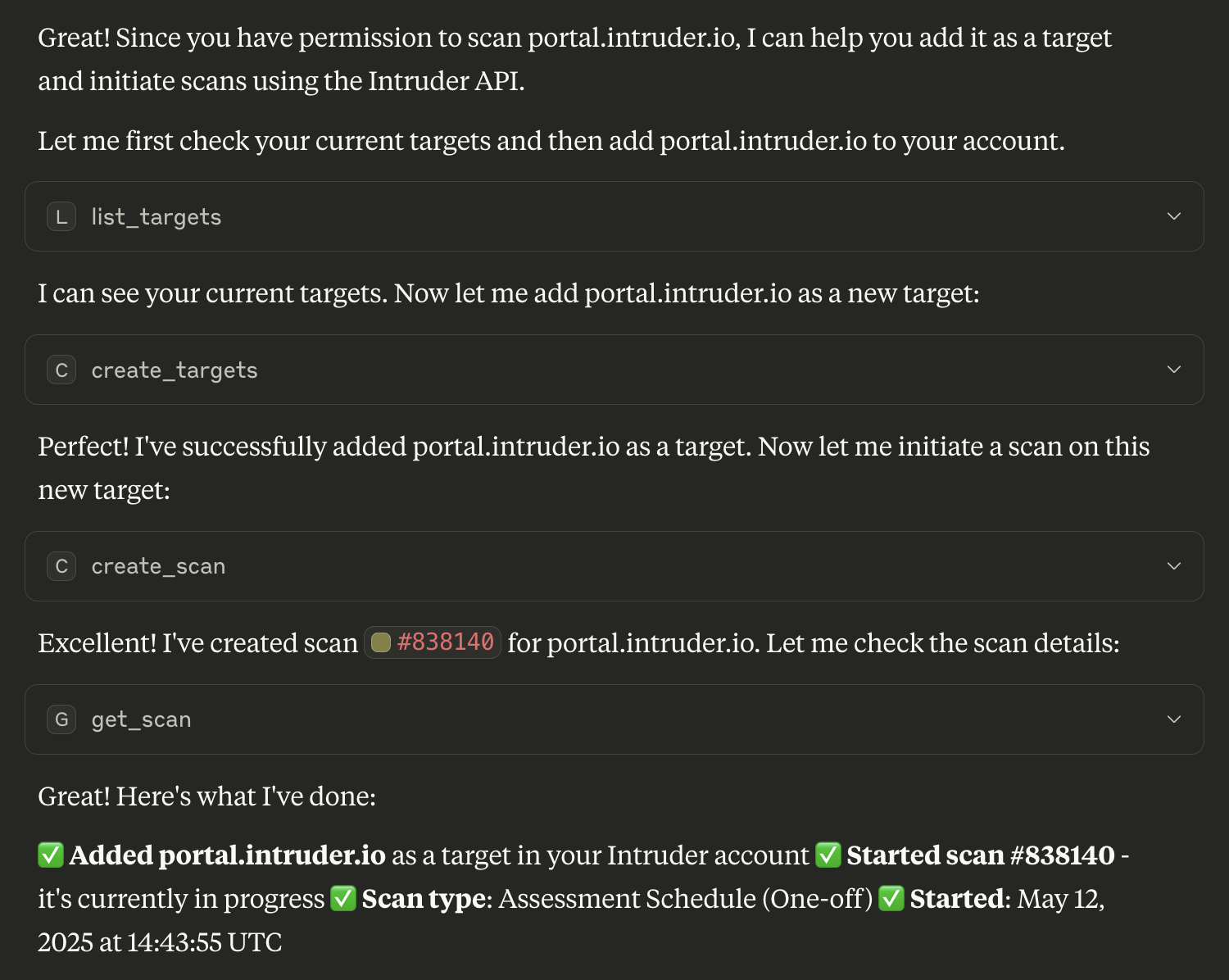
Add and scan targets
Need to assess the security of a new asset? It's as simple as asking:
"Add our new production server prod.example.com to Intruder and run a scan."
The agent will add the target, initiate the scan, and report back with the results.
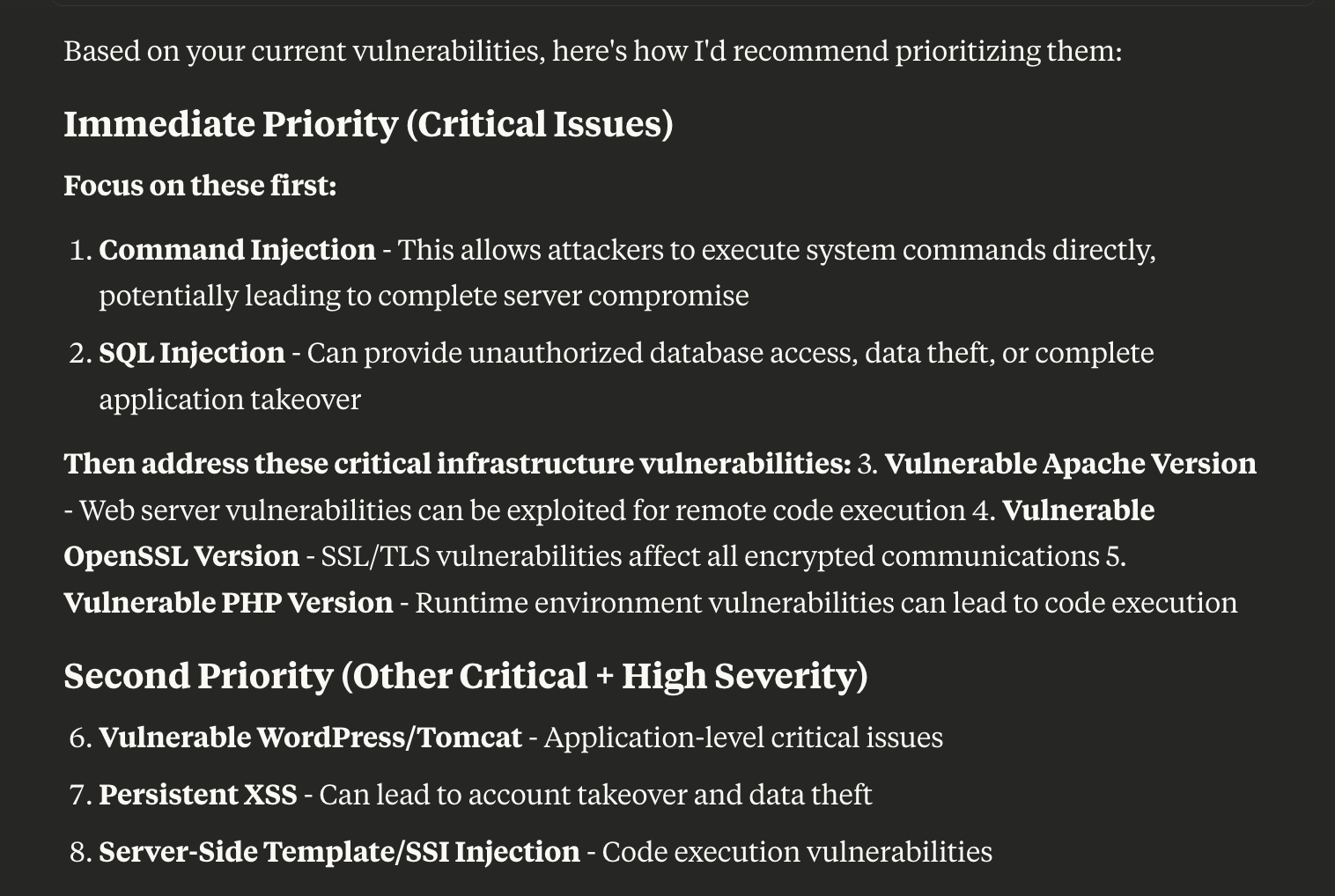
Prioritise issues
Have a conversation with your AI agent to understand which issues to tackle first:
"Show me the critical vulnerabilities for our web apps, and suggest which to prioritise based on exploitability and potential business impact."
The agent can incorporate context like severity, exploit likelihood, and CVSS scores from Intruder to help your team focus on the most pressing risks.
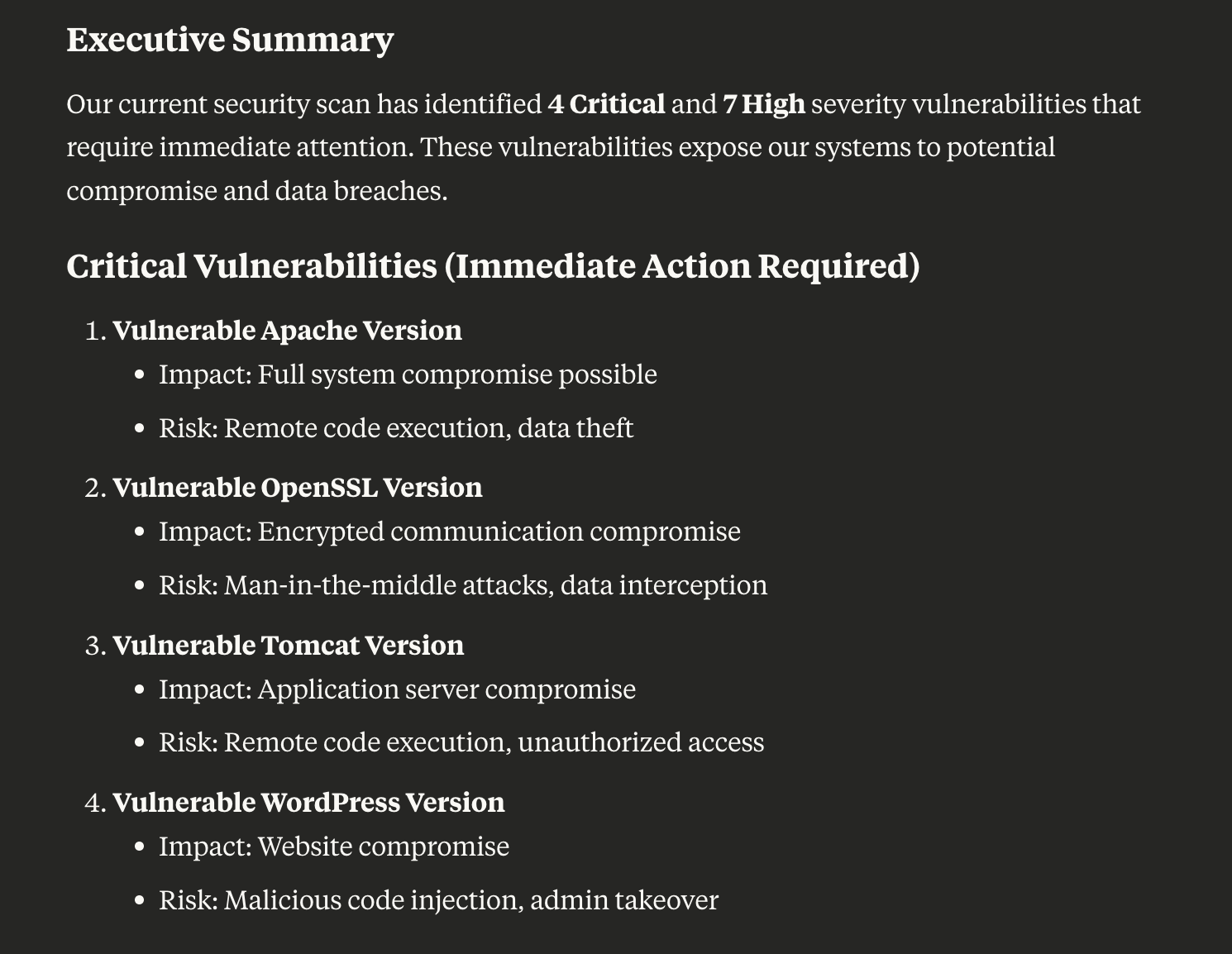
Produce management summaries
Save time by generating stakeholder-ready summaries:
"Summarise our current vulnerabilities for the leadership team, highlighting critical issues and upcoming remediation plans."
The agent generates a concise, business-friendly summary that can be shared directly with stakeholders.
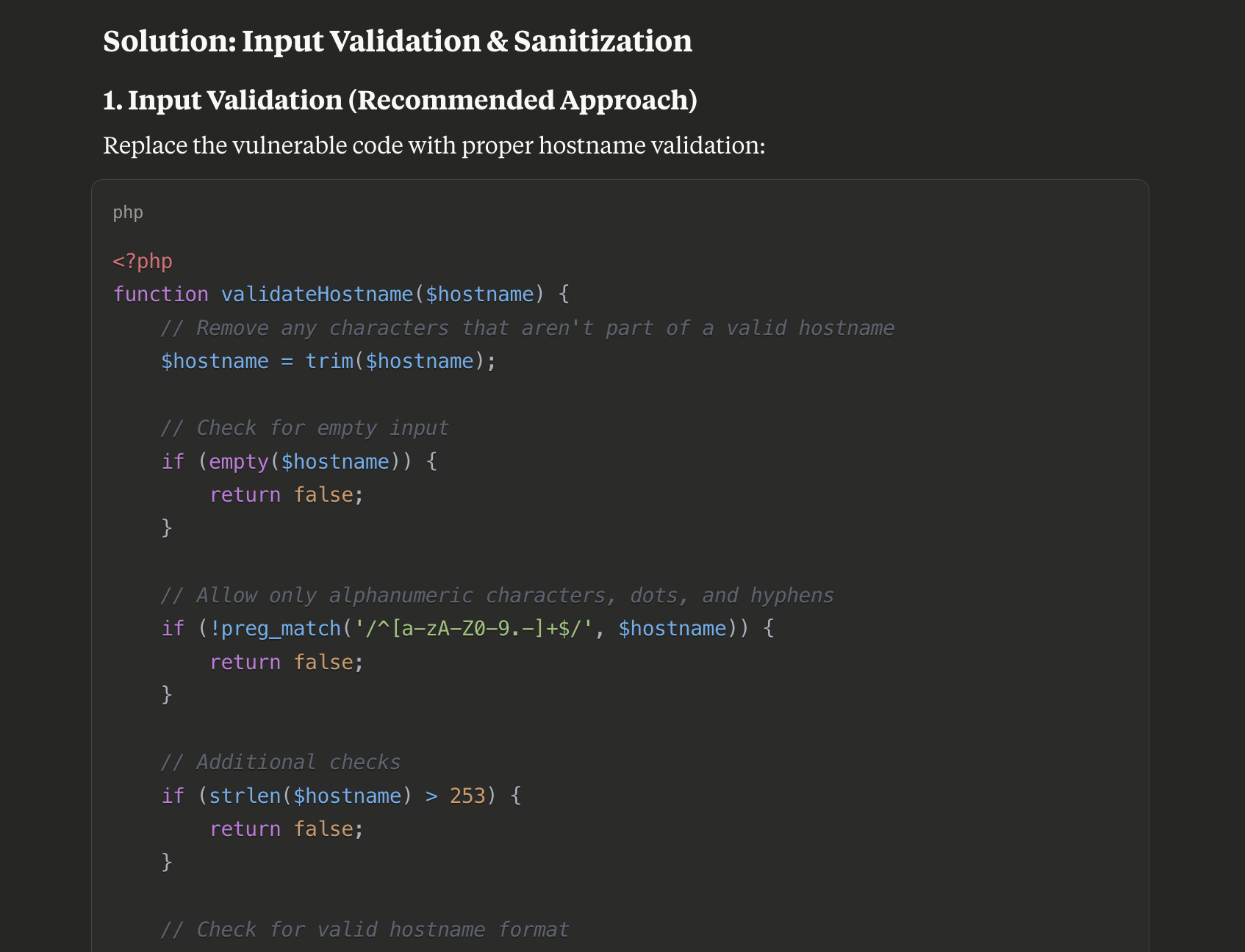
Validate and remediate vulnerabilities
Get hands-on guidance for confirming and fixing findings:
"Guide me through reproducing the SQL injection vulnerability on api.example.com and provide a remediation plan tailored to our tech stack."
The agent retrieves the scanner output and occurrence details, then provides actionable, context-aware remediation advice.
Manage your attack surface
Keep your targets organised and under control:
"Tag all of our staging servers and show me which targets are currently unresponsive."
The agent can list targets by status, apply tags, and give you a clear picture of your attack surface.
Check license usage
Stay on top of your account capacity:
"How many infrastructure and application licenses do we have left?"
The agent retrieves your current license totals and consumption, so you know where you stand before adding new targets.
Snooze issues
Manage noise without losing track of accepted risks:
"Snooze the TLS 1.0 findings on our legacy servers as accepted risk for 90 days."
The agent snoozes the issue with the appropriate reason and duration, keeping your issue list focused on actionable items.
Updated 3 months ago
